EU GMP Annex 11: Patch or Isolate. What's Changing in Cybersecurity for the Pharma Industry
April 7, 2026EU GMP Annex 11: Patch or Isolate
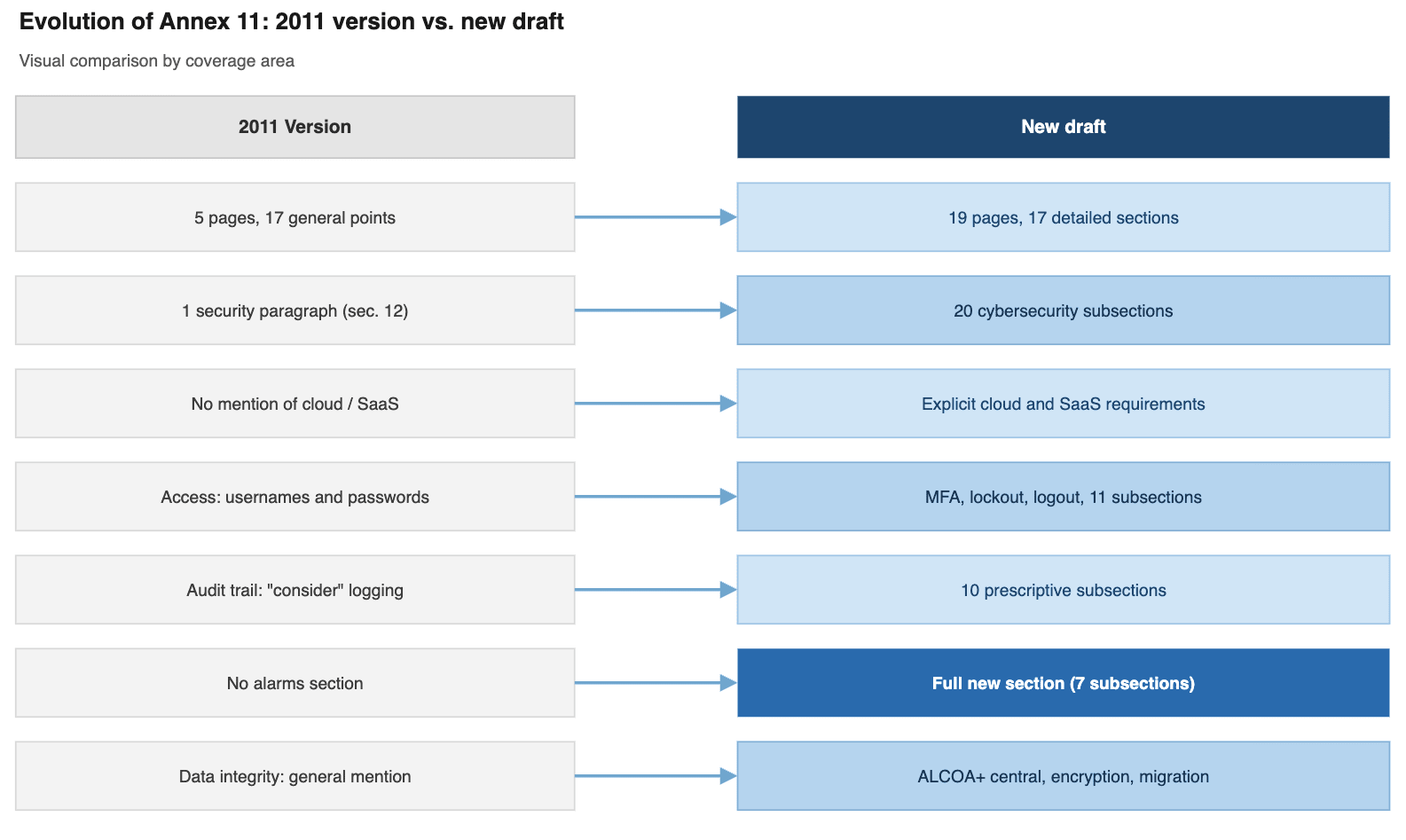
Annex 11 of the GMP guidelines governs computerised systems in pharmaceutical manufacturing. After 14 years without revision, the new draft radically transforms cybersecurity requirements — and sends a very direct message to companies running unpatched systems or legacy platforms.
The rule that changes everything: patch or isolate
If there is one change in the new draft that should concern and mobilise any plant manager, IT lead, or quality professional in the pharmaceutical sector, it is this: The draft establishes that systems running on vendor-unsupported platforms are "highly vulnerable" and must be isolated from networks and the internet (sec. 15.12). The same applies to systems where critical security patches have not been applied in a timely manner. Furthermore, when it comes to critical vulnerabilities, the text leaves no room for interpretation: patching must be immediate (sec. 15.13). In practice, this means that every asset in your plant running an outdated Windows version, an unpatched SCADA system, or a lab server that hasn't received a security update in years becomes a candidate for network disconnection. And if that asset is part of a production process, the operational impact can be significant.
From 1 paragraph to 20 subsections: the new security section
The 2011 version of Annex 11 devoted a single generic clause to "logical and physical" security controls. The new draft deploys a full Section 15 with 20 subsections covering every layer of defence now considered standard in industrial cybersecurity.
Security governance (sec. 15.1–15.3)
Companies must implement and maintain an effective information security management system (sec. 15.1), stay informed about emerging threats and continuously improve protective measures (sec. 15.2), and conduct recurring security awareness training, including simulated exercises such as phishing campaigns (sec. 15.3).
Perimeter and network security (sec. 15.8–15.9, 15.19–15.20)
Networks must be segmented using firewalls enforcing strict rules based on IPs, destinations, protocols, applications, and ports (sec. 15.8). These rules must be reviewed periodically, as they tend to degrade over time — ports get opened and never closed, rules become obsolete as threats evolve (sec. 15.9). For critical systems exposed to the internet, the draft requires periodic penetration testing to assess the adequacy of security measures and identify vulnerabilities (sec. 15.19). Remote connections must use secure, encrypted protocols (sec. 15.20).
Platform management and patching (sec. 15.10–15.14)
This is the section with the greatest operational impact:
- Operating systems and platforms must be updated in a timely manner according to vendor recommendations to prevent their use in an unsupported state (sec. 15.10).
- Application validation on updated platforms and data migration must be planned and completed before vendor support expires (sec. 15.11).
- Systems running on unsupported platforms are highly vulnerable and must be isolated from networks and the internet (sec. 15.12).
- Critical vulnerability patches must be deployed immediately (sec. 15.13).
- Systems without critical patches applied carry a higher risk of data integrity loss and must be isolated (sec. 15.14). The logic is binary: if a system is supported and patched, it can remain on the network. If it is not, it gets isolated. There is no middle ground.
Endpoint protection (sec. 15.15–15.18)
The use of read/write USB devices on GMP servers and workstations must be strictly controlled (sec. 15.15). If a USB device may have been used outside the organisation, it must not be connected without an effective prior scan (sec. 15.16). USB ports on servers and critical systems must be disabled by default, blocked, or physically removed (sec. 15.17). Antivirus software must be installed and continuously updated with the latest definitions (sec. 15.18).
Physical security and continuity (sec. 15.4–15.7)
Servers, workstations, and storage media must be physically protected, with access to server rooms and data centres limited to the minimum necessary and protected by multi-factor authentication (sec. 15.4). Data centres must be built to minimise the risk of natural and man-made disasters (sec. 15.5). Critical data must be automatically replicated to a secondary data centre located at a safe distance (sec. 15.6). A tested disaster recovery plan must exist and be available, with a defined Recovery Time Objective (RTO) (sec. 15.7).
The context: why now
In 2011, when the current version of Annex 11 was published, most pharmaceutical manufacturing systems operated on isolated networks. Ransomware was an emerging threat. Cloud services were barely used in regulated environments.
 Today, pharmaceutical plants operate with connected systems, SaaS platforms, third-party remote access, and an attack surface that grows every year. The draft explicitly acknowledges this shift: "with an ever-evolving IT landscape, increasing use of cloud services and the introduction of new technologies, there is a growing need for updated guidance."
Today, pharmaceutical plants operate with connected systems, SaaS platforms, third-party remote access, and an attack surface that grows every year. The draft explicitly acknowledges this shift: "with an ever-evolving IT landscape, increasing use of cloud services and the introduction of new technologies, there is a growing need for updated guidance."
What does this mean for your organisation?
Although the text is still in draft form, the regulatory direction is unambiguous. Companies that begin assessing their position now will be better prepared:
- System inventory: how many GMP assets are running on unsupported platforms? How many have critical patches pending?
- Isolation capability: if you had to isolate those systems tomorrow, is your network ready to do so without disrupting production?
- Network segmentation: are your OT networks segmented? Are your firewall rules reviewed and up to date?
- Vulnerability management: do you have a defined patching process with response times for critical vulnerabilities?
- Continuity planning: is there a tested disaster recovery plan with a defined RTO?
How infraone can help
At infraone, we specialize in cybersecurity for pharmaceutical industry. We help our clients assess the real state of their GMP systems, identify gaps against the requirements of the new Annex 11 draft, and design remediation plans that are operationally viable. If you want to know how many of your systems would require isolation under the new regulation, get in touch.